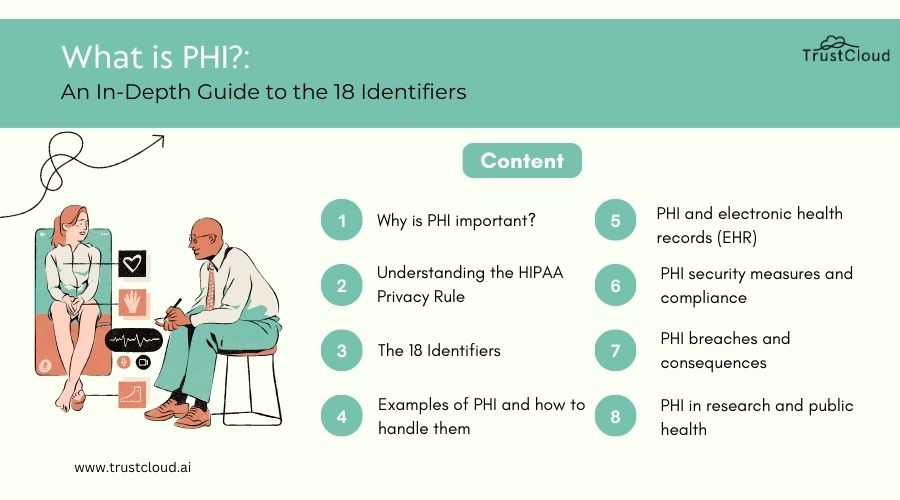
In this article
Securing PHI is essential for maintaining patient privacy, safeguarding sensitive medical data, and complying with regulatory requirements such as the Health Insurance Portability and Accountability Act (HIPAA). To ensure the security of PHI, healthcare organizations must implement a comprehensive approach that addresses administrative, technical, and physical safeguards.
Administrative safeguards involve establishing policies, procedures, and training programs to educate staff on PHI security practices, enforce access controls, and respond to security incidents effectively. Technical safeguards include encryption, access controls, authentication mechanisms, and intrusion detection systems to securing PHI stored electronically from unauthorized access, disclosure, and breaches.
Physical safeguards encompass physical security measures, such as secure storage facilities, access controls, and surveillance systems, to prevent unauthorized access to PHI in paper records or physical storage devices.
Additionally, healthcare organizations should conduct regular risk assessments, audits, and security testing to identify vulnerabilities and mitigate risks for securing PHI. They should also implement incident response plans and data breach notification procedures to address security incidents promptly and minimize the impact on patients and stakeholders.
By implementing robust security measures and adhering to best practices for securing PHI, healthcare organizations can protect patient privacy, maintain regulatory compliance, and uphold trust in the healthcare system.
The realm of healthcare data has always been both a treasure trove of vital information and a battlefield of privacy concerns. At the heart of this domain is Protected Health Information (PHI), a term that encapsulates an individual’s health records along with any other data that can be used to identify them.
Understanding and safeguarding PHI is not just a matter of legal compliance; it’s about preserving the trust and confidentiality that form the bedrock of the patient-care provider relationship. This comprehensive exploration seeks to demystify the components of PHI, delving into its 18 identifiers and offering guidance on maintaining its security.
Introduction to PHI (Protected Health Information)
Protected Health Information, or PHI, is a term that encompasses any information in a medical record or other health-related information that can be used to identify an individual and that was created, used, or disclosed in the course of providing a healthcare service, such as diagnosis or treatment. The significance of PHI extends beyond the clinical data; it includes a wide array of identifiers that, when disclosed without authorization, can lead to privacy violations and identity theft.
In an age where digital transactions are the norm, the importance of securing PHI cannot be overstated. It’s not merely about compliance with laws; it’s about upholding the dignity and privacy of individuals at their most vulnerable.
Understanding the importance of PHI security is crucial in today’s digital age, where data breaches are not just a possibility but a frequent occurrence. The security of PHI is not just a concern for healthcare providers but for anyone who handles personal health information in any capacity. This includes insurance companies, employers, schools, and health information exchanges.
The ramifications of PHI breaches are severe, affecting not just the individuals whose information is compromised but also the institutions responsible for their protection. It’s a matter of public trust as much as it is about legal compliance.
Understanding the importance of PHI security
Securing PHI is paramount for several reasons. First and foremost, it’s about protecting individuals’ privacy and personal data. In an era where information can be easily digitized, copied, and transmitted, the risk of unauthorized access and breaches has escalated. Such incidents can have profound emotional and financial impacts on individuals.
Moreover, institutions that fail to secure PHI adequately face significant legal and financial repercussions. Regulatory bodies such as the Health Insurance Portability and Accountability Act (HIPAA) in the United States impose stringent penalties for non-compliance. Beyond compliance, securing PHI is about maintaining the integrity of the healthcare system. Trust is a critical component of patient-care provider relationships. When patients trust that their information is safe, they are more likely to share it freely, leading to better health outcomes.
The 18 identifiers of PHI
PHI is not limited to medical records and diagnosis information; it encompasses 18 different identifiers that, when collected together, can potentially reveal the identity of an individual. These identifiers range from basic contact information to more specific data related to healthcare provision and billing. Understanding these identifiers is crucial for anyone involved in handling personal health information, as it informs the measures needed to ensure their protection.
- Identifiers Related to Individual Characteristics
Identifiers that fall under individual characteristics include names, geographic subdivisions smaller than a state, dates related directly to an individual (such as birth date, admission and discharge dates, and death dates), and photographs.
These identifiers are often the most easily accessible and, therefore, are at a higher risk of being misused. Ensuring that such data is handled with the utmost confidentiality is crucial in safeguarding an individual’s privacy. - Identifiers Related to Healthcare Provision
This category encompasses any identifiers that pertain to the individual’s physical or mental health condition, the provision of healthcare, or the payment for the provision of healthcare. It includes all medical record numbers, health plan beneficiary numbers, and any other account numbers associated with medical care. These identifiers are sensitive as they can reveal information about an individual’s health status, treatments received, and the nature of their health issues. - Identifiers Related to Payment and Billing
Payment and billing-related identifiers include account numbers, certificate/license numbers, vehicle identifiers and serial numbers, device identifiers and serial numbers, and any other unique identifying numbers or codes. While these may seem indirectly related to healthcare, they are integral to the financial transactions involved in healthcare provision. Unauthorized access to such information can lead to financial fraud and identity theft. - Identifiers Related to Location
Geographic data, including addresses and location coordinates, are crucial identifiers. This information, when combined with other identifiers, can be used to trace the physical locations of individuals, putting their safety and privacy at risk. Ensuring that such information is adequately protected is essential to maintaining the confidentiality. - Identifiers Related to Personal Identification
Social security numbers, passport numbers, and driver’s license numbers are prime examples of identifiers related to personal identification. These are highly sensitive pieces of information that can lead to severe cases of identity theft if mishandled. The protection of these identifiers is a critical aspect of securing PHI. - Identifiers Related to Medical Record Numbers
Medical record numbers are unique to each patient and are used extensively within healthcare systems to track patients’ health records. Given their direct link to individuals’ health information, securing these numbers is paramount in protecting patients’ privacy and the integrity of health information.
The impact of PHI breaches and non-compliance
The consequences of PHI breaches extend far beyond the immediate financial penalties. They erode the trust between patients and healthcare providers, potentially deterring individuals from seeking necessary medical care. Furthermore, institutions found to be non-compliant with PHI regulations face not only hefty fines but also significant damage to their reputation. This can lead to a loss of business and a decrease in patient trust, which are difficult to recover from.
PHI regulations and compliance requirements
Protected Health Information (PHI) regulations and compliance requirements are established to protect the confidentiality, integrity, and security of patient data in healthcare settings. The primary regulation governing PHI in the United States is the Health Insurance Portability and Accountability Act (HIPAA), which sets standards for the protecting and securing PHI by covered entities and their business associates. HIPAA regulations include the Privacy Rule, Security Rule, and Breach Notification Rule, which outline requirements for safeguarding PHI, ensuring patient privacy, and reporting data breaches.
In addition to HIPAA, other regulations and standards may apply, depending on the type of healthcare organization and the nature of its operations. For example, healthcare providers may need to comply with state-specific privacy laws, such as California’s Confidentiality of Medical Information Act (CMIA), in addition to HIPAA requirements. Furthermore, healthcare organizations that handle payment card information may need to comply with the Payment Card Industry Data Security Standard (PCI DSS).
Compliance with this regulations and requirements involves implementing various administrative, technical, and physical safeguards to protect patient data, conducting risk assessments, training staff on privacy and security practices, and regularly auditing and monitoring compliance efforts. Non-compliance with PHI regulations can result in significant penalties, including fines, legal action, and reputational damage, underscoring the importance of adhering to regulatory requirements and maintaining a strong culture of compliance within healthcare organizations.
Navigating the complex landscape of PHI regulations requires a thorough understanding of compliance requirements. Laws such as HIPAA in the United States set the standard for PHI security, outlining specific administrative, physical, and technical safeguards that must be in place to protect sensitive health information. Compliance with these regulations is not optional; it’s a legal obligation for anyone who handles PHI.
Best practices
Adopting best practices for handling PHI is crucial in preventing breaches and ensuring compliance. This includes implementing strong data encryption, conducting regular security risk assessments, and ensuring that only authorized personnel have access to PHI. Training and education play a critical role in reinforcing the importance of PHI security among staff members.
Handling Protected Health Information (PHI) requires adherence to best practices to safeguard patient privacy and ensure compliance with regulations like the Health Insurance Portability and Accountability Act (HIPAA). Some key best practices for securing PHI include:
- Access Control:
Limit access to PHI to authorized personnel only. Implement role-based access controls and user authentication mechanisms to prevent unauthorized access. - Encryption:
Encrypt PHI both in transit and at rest to protect it from unauthorized disclosure. Utilize encryption protocols and secure communication channels to ensure data confidentiality. - Secure Storage:
Store PHI in secure environments, such as encrypted databases or secure servers, with appropriate physical and logical safeguards to prevent unauthorized access or theft. - Data Minimization:
Only collect and retain PHI that is necessary for legitimate business purposes. Minimize the use of PHI in marketing or other non-healthcare-related activities. - Training and Awareness:
Provide regular training and awareness programs for employees on HIPAA regulations, security protocols, and the importance of safeguarding PHI. - Incident Response:
Establish protocols for responding to PHI breaches or security incidents, including reporting requirements, investigation procedures, and mitigation measures. - Business Associate Agreements:
Ensure that business associates and third-party vendors handling PHI sign agreements outlining their responsibilities for securing PHI and complying with HIPAA regulations. - Auditing and Monitoring: Regularly audit and monitor access to PHI, including user activity logs and system activity, to detect and prevent unauthorized access or breaches.
By following these best practices, healthcare organizations can effectively protect PHI, maintain patient trust, and ensure compliance with regulatory requirements.
PHI encryption and data security measures
PHI encryption and data security measures are paramount for safeguarding Protected Health Information from unauthorized access, disclosure, and theft. Encryption involves converting PHI into an unreadable format using cryptographic algorithms, making it accessible only to authorized users with decryption keys. Implementing encryption both in transit and at rest ensures data confidentiality and mitigates the risk of breaches or unauthorized disclosures.
In addition to encryption, healthcare organizations should employ various data security measures to enhance protection. This includes implementing access controls, such as role-based access permissions and user authentication mechanisms, to restrict access to PHI to authorized personnel only. Secure storage solutions, such as encrypted databases and secure servers, should be utilized to store it, with physical and logical safeguards to prevent unauthorized access.
Furthermore, regular auditing and monitoring of access and activity logs are essential for detecting and responding promptly to potential security incidents or breaches. Healthcare organizations should also provide comprehensive training and awareness programs for employees to educate them on the importance of security, HIPAA regulations, and security best practices.
By implementing robust encryption and data security measures, healthcare organizations can mitigate the risk of PHI breaches, protect patient privacy, and ensure compliance with regulatory requirements.
Encrypting PHI is one of the most effective ways to protect it from unauthorized access. Encryption transforms readable data into an encoded format that can only be accessed with a key. Coupled with other security measures such as multi-factor authentication and secure data storage, encryption significantly reduces the risk of PHI breaches.
PHI in electronic health records (EHR)
Protected Health Information (PHI) in Electronic Health Records (EHR) refers to sensitive medical information stored electronically about patients. EHR systems digitize and centralize patient health records, including medical history, diagnoses, treatments, prescriptions, and laboratory results. As PHI in EHR contains personal identifiers, such as names, addresses, and Social Security numbers, it is subject to stringent privacy and security regulations, notably the Health Insurance Portability and Accountability Act (HIPAA).
Healthcare providers are responsible for ensuring the confidentiality, integrity, and availability of EHR systems. This entails implementing robust security measures, including encryption, access controls, audit trails, and regular risk assessments. Additionally, healthcare professionals must adhere to HIPAA regulations regarding disclosure, sharing, and access, ensuring that patient privacy is protected at all times.
Despite challenges related to data breaches and cybersecurity threats, EHR systems offer numerous benefits, such as improved care coordination, enhanced patient outcomes, and streamlined healthcare processes. By effectively managing PHI in EHR, healthcare organizations can leverage technology to deliver high-quality, patient-centered care while safeguarding patient privacy and complying with regulatory requirements.
The advent of Electronic Health Records (EHR) has transformed healthcare, making it easier to store, access, and share health information. However, it also presents new challenges in securing PHI. Ensuring that EHR systems are compliant with PHI regulations and equipped with robust security measures is essential to protecting sensitive health information.
The role of healthcare providers in securing PHI
Healthcare providers play a critical role in protecting Protected Health Information (PHI) and upholding patient privacy and confidentiality. As custodians of sensitive medical information, healthcare providers are entrusted with the responsibility of safeguarding PHI from unauthorized access, disclosure, and misuse.
This involves implementing robust security measures, such as encryption, access controls, and audit trails, to ensure the confidentiality, integrity, and availability of PHI. Healthcare providers must also adhere to regulatory requirements, notably the Health Insurance Portability and Accountability Act (HIPAA), which sets standards for the protection and secure handling of PHI.
Additionally, healthcare professionals are responsible for educating staff members on privacy and security practices, conducting regular training sessions, and enforcing policies and procedures related to PHI protection. By prioritizing patient privacy and adopting best practices for PHI security, healthcare providers can foster trust with patients, maintain regulatory compliance, and mitigate the risk of data breaches or privacy violations. Ultimately, healthcare providers play a pivotal role in protecting PHI and preserving patient confidentiality in today’s digital healthcare landscape.
Healthcare providers are on the front lines of PHI protection. Their role extends beyond the provision of medical care; they are also custodians of sensitive health information. Adopting a culture of compliance and privacy, investing in staff training, and implementing stringent security measures are all crucial to securing PHI.
The role of technology in securing PHI
Technology plays a crucial role in securing PHI by providing tools and solutions to safeguard patient data from unauthorized access, disclosure, and breaches. Encryption technology is a fundamental component of PHI security, as it converts sensitive information into an unreadable format, making it inaccessible to unauthorized users without decryption keys. Additionally, access control mechanisms, such as role-based access controls and user authentication protocols, help restrict access to PHI to authorized personnel only, minimizing the risk of data breaches.
Furthermore, technology enables healthcare organizations to implement robust security measures, such as intrusion detection systems, firewalls, and endpoint security solutions, securing PHI from cyber threats and malware attacks. Regular monitoring and auditing of systems and networks using advanced analytics and threat intelligence tools helps detect and respond to security incidents promptly, mitigating potential risks to patient data.
Moreover, advancements in cloud computing and secure storage solutions provide healthcare organizations with scalable and resilient platforms to store and manage PHI securely. Cloud-based security solutions offer enhanced data protection, encryption, and access controls, enabling healthcare providers to adhere to regulatory requirements and maintain compliance with standards such as the Health Insurance Portability and Accountability Act (HIPAA).
Overall, technology plays a pivotal role in securing PHI by providing innovative solutions, tools, and frameworks to mitigate risks, enhance security posture, and safeguard patient privacy in today’s digital healthcare landscape.
Technology plays a pivotal role in securing PHI. From encryption to blockchain, technological innovations offer new ways to protect health information. However, technology is a double-edged sword; as security measures evolve, so do the tactics of cybercriminals. Staying abreast of technological advancements and their implications for PHI security is imperative.
PHI training and education for healthcare professionals
PHI training and education are essential components of ensuring that healthcare professionals understand their responsibilities in protecting Protected Health Information (PHI) and maintaining patient privacy and confidentiality. Healthcare professionals, including doctors, nurses, administrative staff, and support personnel, handle sensitive patient data on a daily basis and must be equipped with the knowledge and skills necessary to safeguard PHI from unauthorized access, disclosure, and breaches.
Training programs on PHI security should cover a range of topics, including HIPAA regulations, privacy policies and procedures, secure handling and storage of PHI, access controls, encryption techniques, and incident response protocols. These programs should be tailored to the specific roles and responsibilities of different healthcare professionals, ensuring that each individual understands their obligations and the potential consequences of non-compliance with PHI security requirements.
Regular refresher training sessions and updates on changes to regulations or security protocols are also crucial to keeping healthcare professionals informed and up-to-date on best practices for securing PHI. Additionally, incorporating real-life scenarios and case studies into training sessions can help reinforce key concepts and promote a culture of accountability and vigilance in safeguarding patient privacy.
By investing in comprehensive PHI training and education programs, healthcare organizations can empower their staff to effectively protect patient data, uphold regulatory compliance, and maintain trust with patients. Ultimately, well-trained healthcare professionals are instrumental in ensuring the security and confidentiality of PHI in today’s digital healthcare environment.
Training and education are the cornerstones of effective PHI protection. Healthcare professionals must be well-versed in the laws and regulations governing PHI, as well as the best practices for its security. Regular training sessions can help reinforce the importance of PHI protection and keep staff updated on the latest security protocols.
Conclusion: safeguarding PHI for a secure healthcare system
The protection of PHI is not just a legal requirement; it’s a moral obligation to the individuals whose data is entrusted to healthcare providers. Safeguarding this information requires a concerted effort from all stakeholders, including healthcare professionals, technology providers, and regulatory bodies. By embracing best practices, investing in education and technology, and fostering a culture of compliance, we can ensure the security of PHI and maintain the trust that underpins the healthcare system.
To further explore how you can enhance your organization’s governance, risk management, and compliance processes, consider signing up with TrustCloud. Our GRC launchpad offers a wealth of resources and expertise on various GRC topics and compliance standards. Sign up with TrustCloud to learn more about transforming GRC into a profit center through automation and informed decision-making.
